AI deepfakes in this NSFW space: what you’re really facing
Sexualized AI fakes and “undress” images are now affordable to produce, tough to trace, yet devastatingly credible upon viewing. This risk isn’t imaginary: artificial intelligence clothing removal applications and online nude generator platforms are being used for harassment, extortion, and image damage at scale.
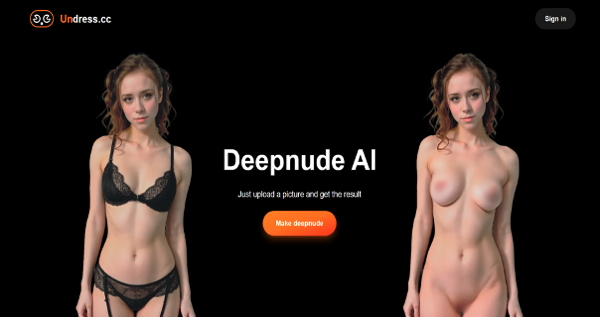
The market advanced far beyond those early Deepnude app era. Today’s NSFW AI tools—often branded as AI strip, AI Nude Creator, or virtual “AI girls”—promise realistic naked images from a single photo. Though when their generation isn’t perfect, they’re convincing enough to trigger panic, coercion, and social backlash. Across platforms, individuals encounter results through names like various services including N8ked, DrawNudes, UndressBaby, AINudez, Nudiva, and PornGen. The tools vary in speed, authenticity, and pricing, yet the harm pattern is consistent: unwanted imagery is produced and spread faster than most individuals can respond.
Tackling this requires paired parallel skills. Initially, learn to detect nine common red flags that betray AI manipulation. Next, have a reaction plan that emphasizes evidence, fast escalation, and safety. What follows is a actionable, experience-driven playbook used within moderators, trust plus safety teams, plus digital forensics experts.
How dangerous have NSFW deepfakes become?
Accessibility, believability, and amplification combine to raise overall risk profile. Such “undress app” tools is point-and-click simple, and social sites can spread any single fake across thousands of users before a takedown lands.
Low friction constitutes the core issue. A single selfie can be scraped from a profile and fed through a Clothing Undressing Tool within minutes; some generators additionally automate batches. Quality is inconsistent, but extortion doesn’t require photorealism—only plausibility and shock. External coordination in encrypted chats and file dumps further expands reach, and many hosts sit away from major jurisdictions. This result is rapid whiplash undressbaby.eu.com timeline: generation, threats (“send more or we share”), and distribution, often before a individual knows where to ask for support. That makes recognition and immediate action critical.
The 9 red flags: how to spot AI undress and deepfake images
Most clothing removal deepfakes share common tells across physical features, physics, and environmental cues. You don’t must have specialist tools; train your eye upon patterns that generators consistently get incorrect.
First, look for edge irregularities and boundary problems. Clothing lines, straps, and seams frequently leave phantom imprints, with skin seeming unnaturally smooth while fabric should have compressed it. Accessories, especially chains and earrings, might float, merge with skin, or disappear between frames of a short clip. Tattoos and blemishes are frequently missing, blurred, or displaced relative to source photos.
Second, scrutinize lighting, shadows, and reflections. Shadows under breasts or along the chest area can appear airbrushed or inconsistent against the scene’s lighting direction. Reflections in mirrors, glass, or glossy objects may show initial clothing while such main subject appears “undressed,” a high-signal inconsistency. Specular highlights on flesh sometimes repeat in tiled patterns, such subtle generator signature.
Additionally, check texture realism and hair natural behavior. Body pores may seem uniformly plastic, showing sudden resolution changes around the torso. Body hair plus fine flyaways by shoulders or the neckline often merge into the background or have artificial borders. Hair pieces that should overlap the body could be cut off, a legacy artifact from segmentation-heavy processes used by several undress generators.
Next, assess proportions and continuity. Suntan lines may stay absent or synthetically applied on. Breast form and gravity can mismatch age plus posture. Fingers pressing into the body should compress skin; many synthetics miss this subtle pressure. Fabric remnants—like a material edge—may imprint onto the “skin” through impossible ways.
Fifth, examine the scene background. Boundaries tend to avoid “hard zones” like armpits, hands touching body, or when clothing meets skin, hiding generator failures. Background logos or text may warp, and EXIF data is often deleted or shows editing software but not the claimed source device. Reverse image search regularly shows the source photo clothed on another site.
Sixth, evaluate motion signals if it’s moving content. Breath doesn’t affect the torso; clavicle and rib movement lag the audio; and physics governing hair, necklaces, along with fabric don’t react to movement. Facial swaps sometimes show blinking at odd timing compared with normal human blink patterns. Room acoustics plus voice resonance may mismatch the displayed space if sound was generated plus lifted.
Seventh, examine duplicates plus symmetry. AI favors symmetry, so you may spot repeated skin blemishes reflected across the form, or identical wrinkles in sheets showing on both edges of the image. Background patterns occasionally repeat in artificial tiles.
Eighth, look for user behavior red flags. Fresh profiles with minimal history that abruptly post NSFW “leaks,” aggressive DMs seeking payment, or unclear storylines about how a “friend” acquired the media signal a playbook, rather than authenticity.
Ninth, center on consistency across a set. While multiple “images” showing the same subject show varying physical features—changing moles, absent piercings, or different room details—the chance you’re dealing encountering an AI-generated collection jumps.
What’s your immediate response plan when deepfakes are suspected?
Preserve evidence, stay composed, and work two tracks at simultaneously: removal and limitation. Such first hour matters more than any perfect message.
Start with documentation. Capture entire screenshots, the URL, timestamps, usernames, along with any IDs within the address bar. Save original messages, including demands, and record screen video to show scrolling context. Never not edit the files; store them in a secure directory. If extortion gets involved, do avoid pay and don’t not negotiate. Extortionists typically escalate following payment because such response confirms engagement.
Additionally, trigger platform and search removals. Report the content via “non-consensual intimate media” or “sexualized deepfake” if available. File intellectual property takedowns if this fake uses individual likeness within some manipulated derivative from your photo; several hosts accept these even when this claim is contested. For ongoing protection, use a hashing service like blocking services to create unique hash of personal intimate images and targeted images) allowing participating platforms may proactively block additional uploads.
Inform trusted contacts while the content targets your social connections, employer, plus school. A short note stating the material is fabricated and being handled can blunt rumor-based spread. If the subject is any minor, stop immediately and involve legal enforcement immediately; treat it as emergency child sexual abuse material handling and do not share the file additionally.
Finally, consider legal pathways where applicable. Relying on jurisdiction, you may have claims under intimate photo abuse laws, impersonation, harassment, defamation, and data protection. One lawyer or community victim support agency can advise on urgent injunctions plus evidence standards.
Platform reporting and removal options: a quick comparison
Nearly all major platforms block non-consensual intimate imagery and deepfake porn, but policies and workflows vary. Act quickly and file on all surfaces where this content appears, including mirrors and redirect hosts.
| Platform | Primary concern | Reporting location | Response time | Notes |
|---|---|---|---|---|
| Facebook/Instagram (Meta) | Unwanted explicit content plus synthetic media | App-based reporting plus safety center | Hours to several days | Participates in StopNCII hashing |
| Twitter/X platform | Non-consensual nudity/sexualized content | Profile/report menu + policy form | Variable 1-3 day response | Requires escalation for edge cases |
| TikTok | Sexual exploitation and deepfakes | Built-in flagging system | Quick processing usually | Prevention technology after takedowns |
| Unwanted explicit material | Community and platform-wide options | Community-dependent, platform takes days | Pursue content and account actions together | |
| Independent hosts/forums | Abuse prevention with inconsistent explicit content handling | Contact abuse teams via email/forms | Unpredictable | Leverage legal takedown processes |
Your legal options and protective measures
The law remains catching up, while you likely possess more options compared to you think. You don’t need must prove who created the fake to request removal through many regimes.
In the UK, distributing pornographic deepfakes without consent is a criminal offense through the Online Protection Act 2023. In EU EU, the Artificial Intelligence Act requires identifying of AI-generated content in certain circumstances, and privacy laws like GDPR facilitate takedowns where processing your likeness misses a legal basis. In the United States, dozens of regions criminalize non-consensual explicit content, with several including explicit deepfake provisions; civil claims for defamation, intrusion into seclusion, or right of publicity frequently apply. Many jurisdictions also offer fast injunctive relief when curb dissemination as a case advances.
If any undress image became derived from individual original photo, intellectual property routes can help. A DMCA notice targeting the derivative work or such reposted original frequently leads to more immediate compliance from hosting providers and search indexing services. Keep your requests factual, avoid excessive assertions, and reference the specific URLs.
Where service enforcement stalls, escalate with appeals mentioning their stated policies on “AI-generated explicit content” and “non-consensual intimate imagery.” Persistence matters; multiple, well-documented submissions outperform one vague complaint.
Risk mitigation: securing your digital presence
People can’t eliminate risk entirely, but users can reduce vulnerability and increase personal leverage if some problem starts. Consider in terms of what can be scraped, how material can be remixed, and how quickly you can respond.
Harden your profiles by restricting public high-resolution images, especially straight-on, clearly lit selfies that undress tools prefer. Consider subtle watermarking within public photos while keep originals stored so you may prove provenance during filing takedowns. Check friend lists plus privacy settings within platforms where random users can DM plus scrape. Set establish name-based alerts within search engines along with social sites when catch leaks promptly.
Create an evidence collection in advance: a template log containing URLs, timestamps, along with usernames; a protected cloud folder; and a short explanation you can give to moderators detailing the deepfake. If you manage brand or creator accounts, consider C2PA media Credentials for fresh uploads where possible to assert provenance. For minors in your care, restrict down tagging, block public DMs, plus educate about exploitation scripts that initiate with “send a private pic.”
At work or academic institutions, identify who oversees online safety problems and how fast they act. Pre-wiring a response path reduces panic plus delays if people tries to distribute an AI-powered “realistic nude” claiming it’s you or a peer.
Did you know? Four facts most people miss about AI undress deepfakes
Most deepfake content across platforms remains sexualized. Several independent studies during the past recent years found that the majority—often over nine in ten—of detected deepfakes are pornographic plus non-consensual, which aligns with what websites and researchers observe during takedowns. Digital fingerprinting works without revealing your image publicly: initiatives like hash protection services create a digital fingerprint locally plus only share such hash, not original photo, to block future uploads across participating platforms. EXIF metadata infrequently helps once content is posted; leading platforms strip it on upload, so don’t rely through metadata for provenance. Content provenance standards are gaining ground: C2PA-backed authentication systems can embed authenticated edit history, enabling it easier to prove what’s genuine, but adoption stays still uneven within consumer apps.
Quick response guide: detection and action steps
Pattern-match for the nine tells: boundary anomalies, lighting mismatches, texture and hair anomalies, proportion errors, background inconsistencies, motion/voice mismatches, mirrored repeats, concerning account behavior, and inconsistency across a set. When people see two and more, treat such content as likely synthetic and switch to response mode.
Record evidence without resharing the file broadly. Report on every service under non-consensual intimate imagery or explicit deepfake policies. Use copyright and data protection routes in together, and submit a hash to some trusted blocking platform where available. Inform trusted contacts with a brief, factual note to prevent off amplification. If extortion or underage individuals are involved, report to law enforcement immediately and avoid any payment or negotiation.
Above all, act quickly while being methodically. Undress generators and online adult generators rely through shock and speed; your advantage remains a calm, documented process that triggers platform tools, enforcement hooks, and social containment before a fake can define your story.
For clarity: references about brands like various services including N8ked, DrawNudes, UndressBaby, explicit AI tools, Nudiva, and similar generators, and similar AI-powered undress app or Generator services remain included to explain risk patterns while do not support their use. Our safest position is simple—don’t engage regarding NSFW deepfake production, and know ways to dismantle synthetic media when it targets you or people you care for.

